CYBERCRIME INCIDENT REPORT
Confidential — For Authorized Personnel Only
1. Executive Summary
This report documents a series of suspected cyber-related incidents affecting private online game servers. The purpose of this report is to record technical observations, community reports, and collected evidence related to repeated server disruptions and exploit attempts. Server administrators and members of the gaming community have reported multiple suspicious activities including exploit attempts, abnormal gameplay behavior, excessive packet traffic, repeated automated actions, and server disruption events. Some incidents involved tools commonly used for packet manipulation and repeated command execution, which resulted in instability and performance issues on the affected servers.
2. Observed Activities
- !Repeated exploit attempts affecting gameplay mechanics
- !Abnormal packet traffic sent to the server in large volumes
- !Automated or repeated commands causing server instability
- !Excessive in-game spawning behavior leading to server lag
- !Network traffic spikes consistent with service disruption attempts
3. Incident Investigation Timeline
| Date | Attacker Alias / Account | Activity Observed | Evidence Collected |
|---|---|---|---|
| March 2026 | Hao / John Mar Sales | Multiple suspicious login attempts and abnormal packet traffic directed at server login services | Server authentication logs, IP activity records |
| March 2026 | Yumehax | Reported packet-editing tool usage to manipulate in-game actions and perform exploit testing | Gameplay recordings, packet monitoring logs |
| March 2026 | Roms | Server disruption associated with repeated network traffic spikes consistent with denial-of-service behavior | Network monitoring data, server performance logs |
| March 2026 | Renzo Lomosad | Abnormal gameplay behavior including repeated pet spawning and exploit attempts | In-game screenshots, gameplay logs |
| March 2026 | Turbo | Account linked to repeated automated actions and suspicious packet requests | Account activity logs, packet inspection data |
| March 2026 | Multiple reported aliases | Repeated exploit attempts using packet manipulation and automated commands | Combined server logs, security monitoring reports |
| March 2026 | Ongoing monitoring | Continued detection of large volumes of packets sent to the server and repeatable exploit attempts | Firewall logs, network traffic records |
4. Under Monitoring — Observed Aliases
Aliases and accounts that have appeared in community reports or server discussions. Being listed does not imply guilt or confirmed involvement — it is a precautionary categorization for documentation and observation purposes only.
| Alias / Account | Status | Notes |
|---|---|---|
| Hao / John Mar Sales | Under Monitoring | Appeared in community reports and server activity logs. Monitoring ongoing for suspicious behavior. |
| John Wilfred Duran | Under Monitoring | Mentioned in reports and discussions; no confirmed technical attacks observed yet. |
| Roms | Under Monitoring | Observed in reports and server activity; monitoring continues. |
| Renzo Lomosad | Under Monitoring | Appeared in reports and discussions; no verified exploit or attack detected. |
| Yumehax | Under Monitoring | Community reports mention this alias; under observation for possible suspicious activity. |
| Turbo | Under Monitoring | Appeared in multiple incident reports; monitoring ongoing for unusual account behavior. |
| Mharck Jhim Lim | Under Monitoring | Alleged leader figure mentioned in reports; no confirmed attack activity observed. |
5. Monitoring Matrix — Threat Actor Relationship Map
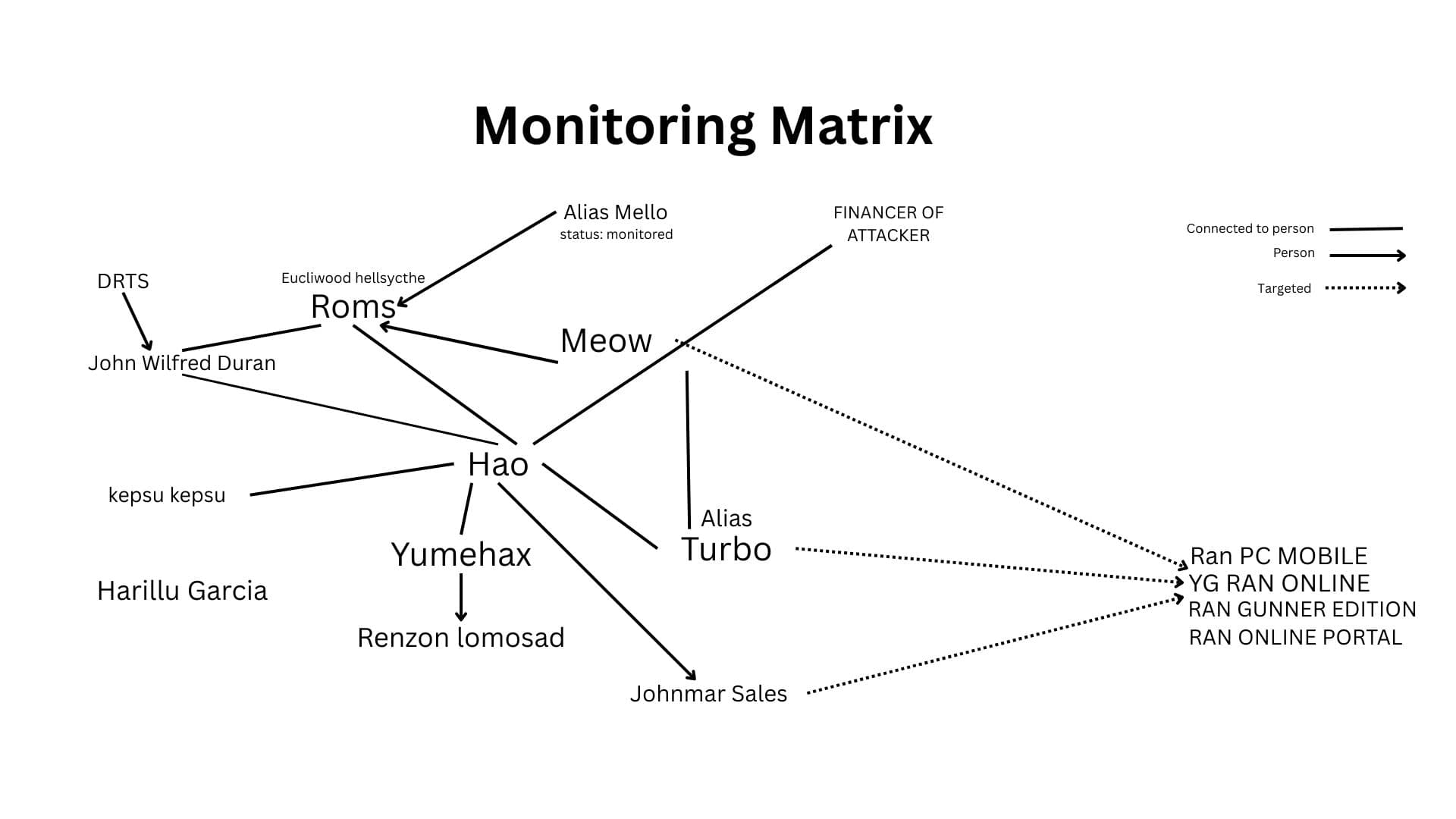
Figure 1: Monitoring Matrix showing connections between observed aliases, associated persons, and targeted servers (Ran PC Mobile, YG Ran Online, Ran Gunner Edition, Ran Online Portal). Legend: Solid arrows = Connected to person | Dashed arrows = Targeted systems.
Key Persons
- Roms — Real name: Eucliwood Hellsycthe, connected to John Wilfred Duran (DRTS), kepsu kepsu
- Hao — Connected to Roms; associated with alias Meow (Alias Mello, status: monitored, Financer of Attacker)
- Yumehax — Connected to Harillu Garcia, Renzon Lomosad
- Turbo — Alias of Hao; targeted multiple game servers
Targeted Servers
- Ran PC Mobile
- YG Ran Online
- Ran Gunner Edition
- Ran Online Portal
6. Technical Analysis — Packet Manipulation & WPE Attacks
What is WPE?
Winsock Packet Editor (WPE) is a tool that allows users to intercept, modify, and send network packets between a client and a server. While originally intended for debugging, it has been exploited to manipulate game behavior, gain unfair advantages, or disrupt server operations.
Detection Methods
- Traffic Analysis: Monitoring abnormal spikes in packet volume
- Behavior Logs: Observing repeated or impossible in-game actions
- IP / Account Tracking: Identifying accounts sending excessive packets
- Rate-Limiting / Firewalls: Blocking rapid packet sends
Packet Editing
Modifying outgoing/incoming packets to change game actions — damage, speed, item spawns.
Packet Flooding
Sending large volumes of packets in short periods to overwhelm the server, causing lag or downtime.
Automated Attacks
Scripts or macros used with WPE to repeatedly send specific commands — pet spawning, item duplication.
Packet Injection
Modifying packets to test for server vulnerabilities, risking server stability.
7. Evidence Collected
8. Law Enforcement Monitoring & Legal Notice
Certain incidents affecting private online game servers — including suspected repeated exploit attempts, packet manipulation, and DDoS-like traffic — are under observation by law enforcement authorities in the Philippines.
Cybercrime Prevention Act of 2012 (RA 10175)
Illegal access to computer systems or data
Illegal interception of communications or data
Data interference (altering, deleting, or damaging data)
System interference (hindering functioning of a system, including DDoS)
Other computer-related offenses (unauthorized use of automated tools or exploits)
Evidence Collection
Server logs, network traffic monitoring, incident reports and screenshots — all documented and may be provided to law enforcement.
Ongoing Legal Action
Incidents may be reviewed and prosecuted under the Cybercrime Prevention Act of 2012. Authorities retain the right to pursue legal action even for attacks targeting private servers.
Community Awareness
Players and administrators should maintain proper logging, report suspicious activity, and avoid tools or scripts that may compromise server security.